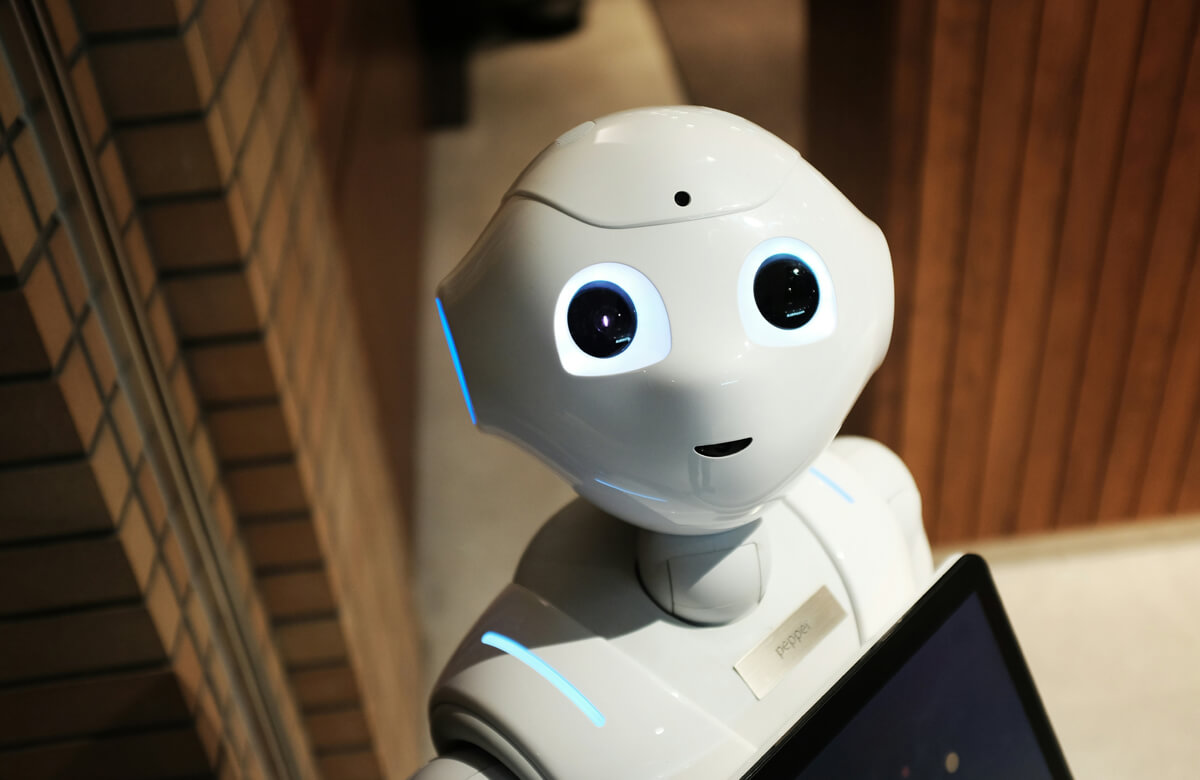
As IoT ecosystems scale rapidly, so do the vulnerabilities. With nearly 20 billion connected devices in circulation—and projections pointing to double that by 2034—the attack surface for cyber criminals is expanding at an alarming rate. One in three data breaches now involves an IoT device, underscoring the urgent need for robust, adaptive security strategies.
📉 Why IoT Devices Are Prime Targets?
Connected devices often lack the hardened security frameworks found in traditional IT infrastructure. Their limited processing power, outdated firmware, and low visibility make them ideal entry points for attackers. Notably:
- IoT devices have been exploited in large-scale VoIP breaches affecting over 1,200 organizations
- They’re frequently used in DDoS attacks due to their accessibility and network reach
- AI is a double-edged sword—enhancing threat detection while also enabling more sophisticated attacks
⚠️ Barriers to Effective IoT Securit
Organizations face four persistent challenges:
- Legacy Systems: Outdated firmware and hardware limit security upgrades
- Low Compute Capacity: Devices can’t support advanced security protocols
- Visibility Gaps: Lack of centralized monitoring across device networks
- Fragmented Architectures: Siloed systems hinder unified threat response
✅ Six Best Practices for IoT Data Protection
We recommend a multi-layered, proactive approach:
- Device Hardening: Secure firmware updates and disable unused ports
- Network Segmentation: Isolate IoT devices from core systems
- Continuous Monitoring: Use real-time analytics to detect anomalies
- Authentication Protocols: Implement strong identity verification
- Data Encryption: Encrypt data at rest and in transit
- Incident Response Planning: Prepare for breaches with defined protocols
🚀 Emerging Technologies to Watch
To future-proof your IoT security posture, consider integrating:
Technology | Strategic Benefit |
|---|---|
AI-driven Security | Real-time anomaly detection and automated threat response |
Zero Trust | Continuous authentication across users and devices |
Blockchain | Decentralized identity management and immutable audit trails |
5G Connectivity | Enhanced encryption, network slicing, and faster, more secure device communication |
🧭 Final Thought
Securing connected devices isn’t just a technical challenge—it’s a strategic imperative. As IoT networks grow, so must your defenses. Eminent Space’s tailored solutions combine deep industry expertise with cutting-edge technologies to help you stay ahead of evolving threats.




